Decoding the Timing of Windows K2 and Linux Copy Fail (The Offensive Algorithm)
We assume corporate cybersecurity is purely a defensive game of patching inevitable software leaks. In reality artificial intelligence is transforming digital security into an aggressive offensive strategy where timing is absolutely everything.
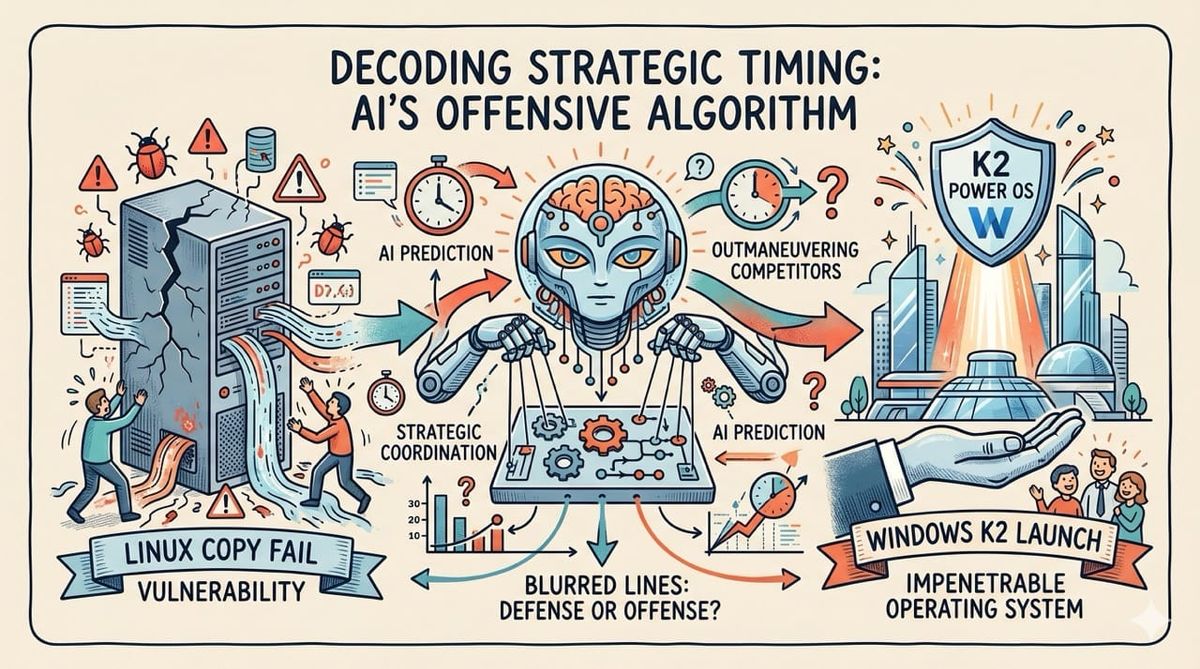
The sudden exposure of massive open source vulnerabilities right as a competitor launches an impenetrable operating system is rarely a coincidence. We are entering an era where artificial intelligence allows massive corporations to completely anticipate and outmaneuver their digital rivals.
Inspiration: Analyzing the highly suspicious timing between the devastating Linux Copy Fail vulnerability and the announcement of the new Microsoft K2 operating system. Realizing that advanced artificial intelligence has completely blurred the lines between defensive preparation and offensive corporate strategy.

The Emerging Threats
The technology industry is currently reeling from the massive Linux Copy Fail vulnerability which fundamentally compromises core file transfer protocols.
Simultaneously Microsoft recently announced their revolutionary K2 operating system which is built entirely from the ground up to prevent these exact types of deep systemic breaches.
This sudden convergence of a massive open source failure and a perfectly timed corporate solution demands deep strategic analysis.
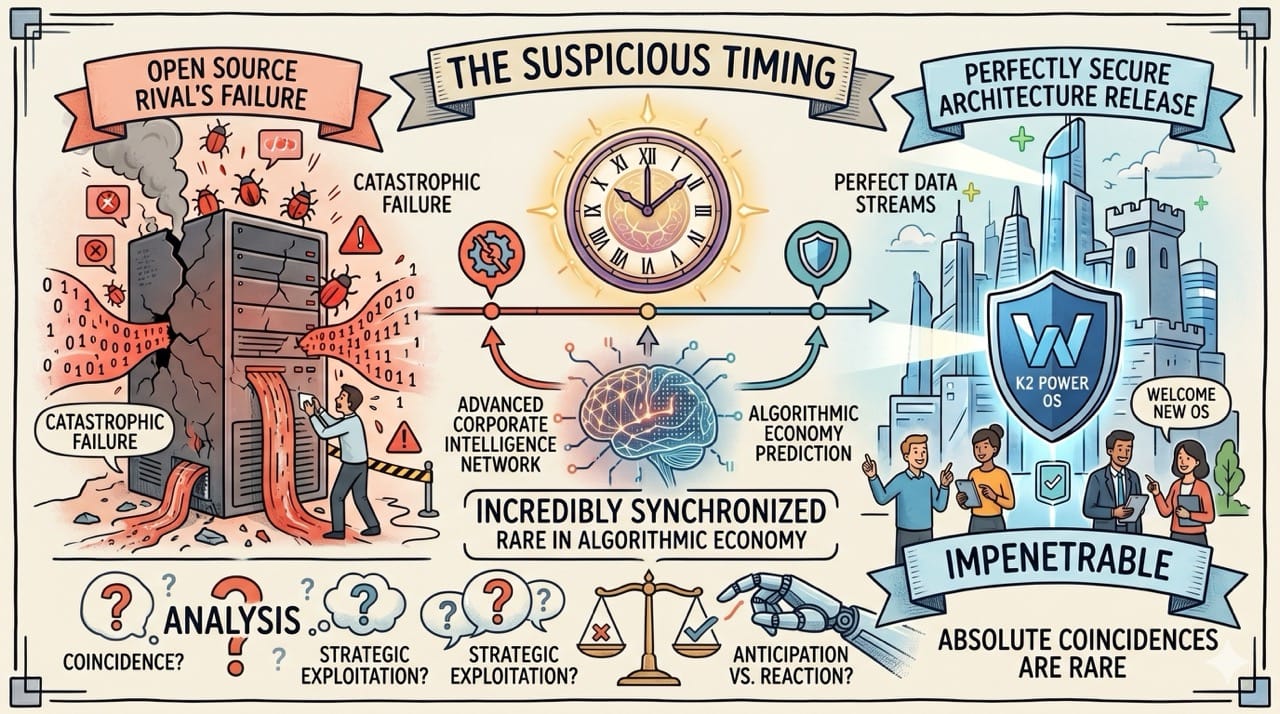
The Suspicious Timing
The chronological proximity of these two massive digital events immediately raises profound questions regarding advanced corporate intelligence.
Releasing a perfectly secure architecture exactly when your biggest open source rival experiences a catastrophic failure feels incredibly synchronized.
In the modern algorithmic economy absolute coincidences of this magnitude are exceptionally rare.
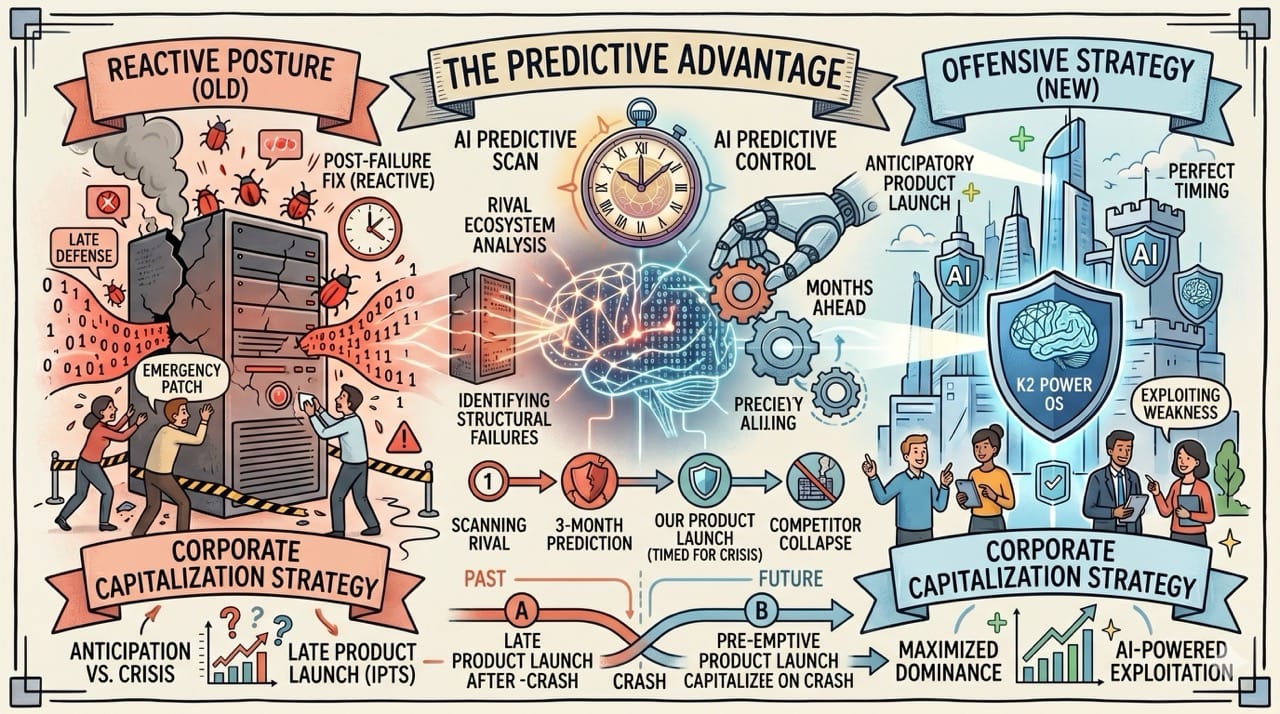
The Predictive Advantage
Cybersecurity has fundamentally shifted from a reactive defensive posture into a highly predictive offensive discipline.
Artificial intelligence algorithms can constantly scan rival ecosystems to precisely identify impending structural failures months before they actually happen.
This allows massive corporations to perfectly time their own product launches to capitalize on the exact moment their competitor inevitably collapses.
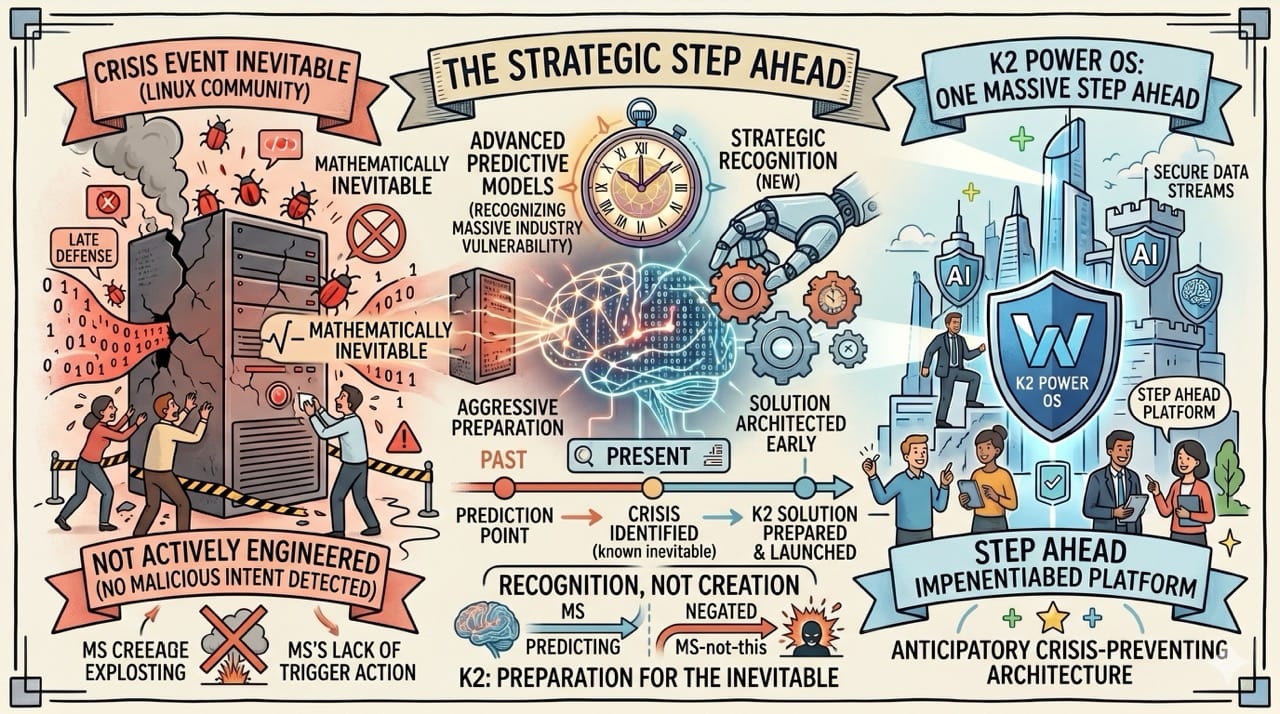
The Strategic Step Ahead
This incredible timing does not necessarily mean Microsoft actively engineered a malicious attack against the global Linux community.
It simply suggests they utilized advanced predictive models to recognize a massive incoming industry vulnerability and aggressively prepared a solution.
They built the K2 architecture specifically to be one massive step ahead of an impending crisis they knew was mathematically inevitable.
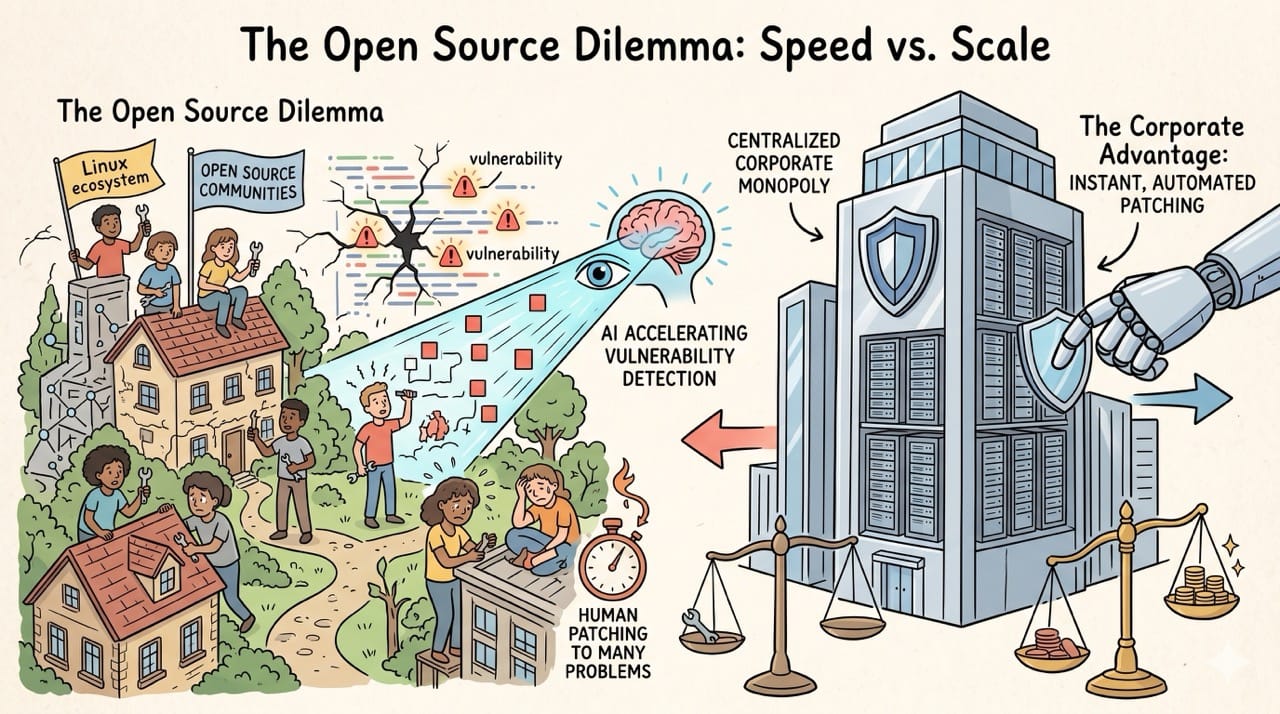
The Open Source Dilemma
The global Linux ecosystem relies entirely on decentralized communities constantly auditing massive libraries of open source code.
As artificial intelligence drastically accelerates the speed of vulnerability detection human volunteers simply cannot patch these complex systems fast enough.
This creates a massive structural advantage for centralized corporate monopolies possessing absolutely unlimited computational resources.
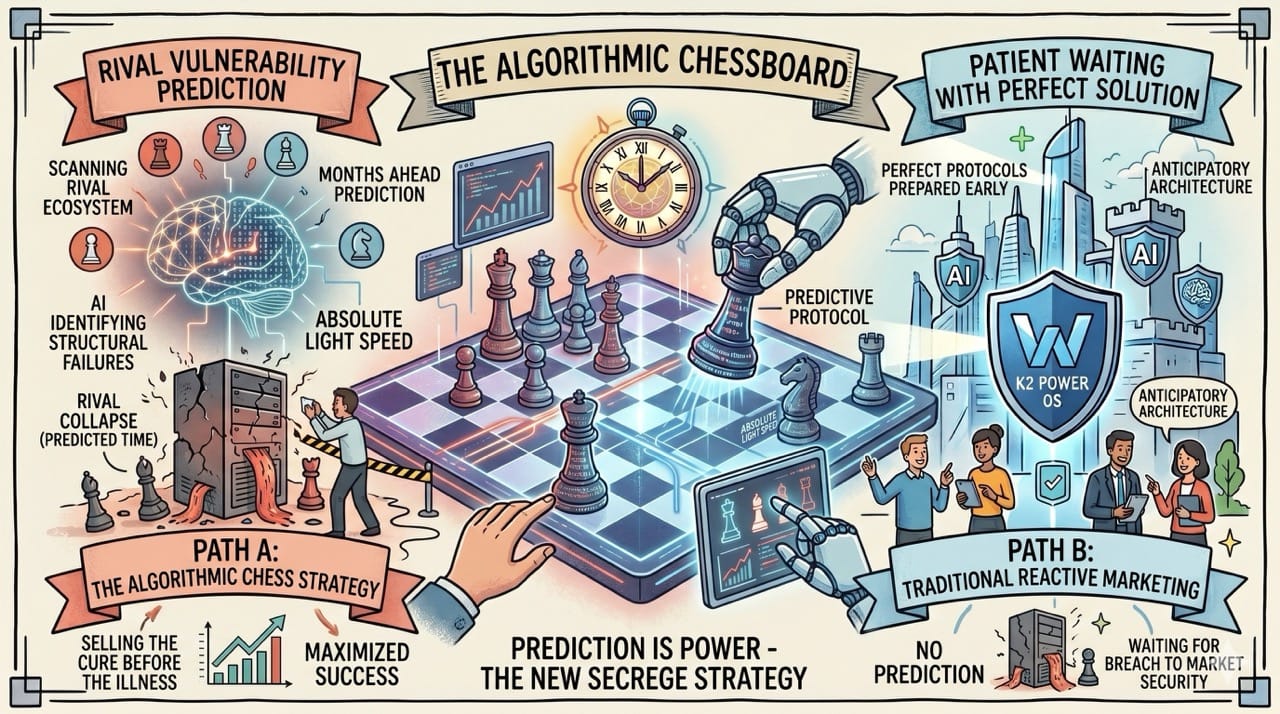
The Algorithmic Chessboard
The future of global digital security is essentially a massive game of algorithmic chess played at absolute light speed.
Companies will no longer wait for a breach to occur before heavily marketing their advanced security protocols.
They will simply use artificial intelligence to predict the exact moment a rival will stumble and patiently wait with the perfect solution.
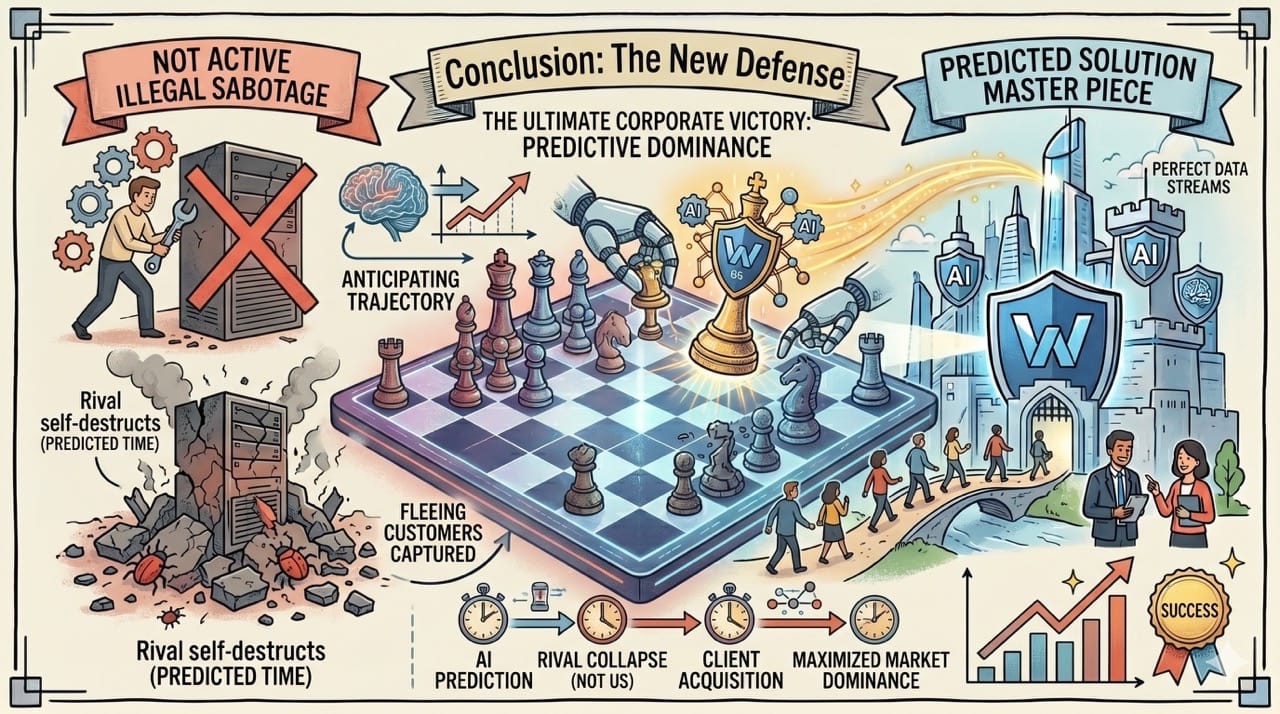
Conclusion: The New Defense
An intelligent observer must recognize that true security requires anticipating the precise trajectory of your fiercest competitor.
The ultimate corporate victory does not require actively destroying your rival through illegal sabotage.
You simply need an algorithm smart enough to predict exactly when they will destroy themselves and be completely ready to capture their fleeing customers.