Defeating Modern OSINT Surveillance: The Architecture of Invisibility
We assume digital privacy is simply a matter of hiding our social media profiles from public view. In reality, evading modern open source intelligence requires a highly technical architecture of data poisoning and strict hardware compartmentalization.
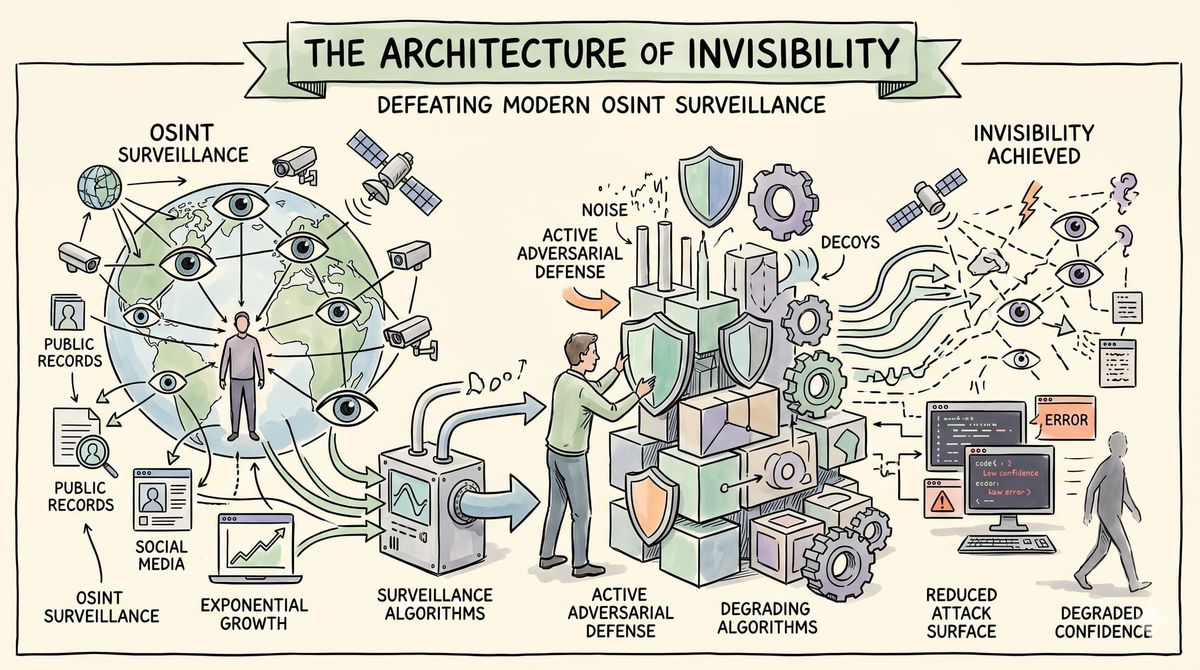
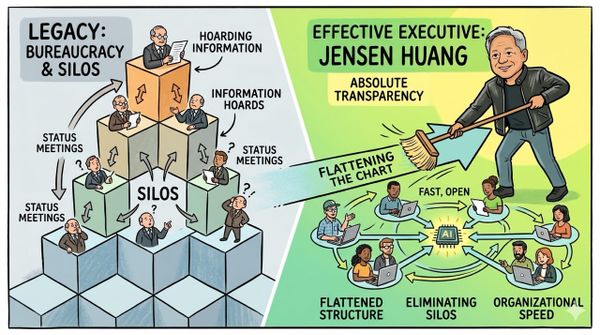
State level surveillance methodologies are now commercially available to anyone with an internet connection. Protecting your finite time and digital identity requires moving from passive hygiene to active adversarial defense.
Inspiration: Analyzing the exponential growth of the open source intelligence market and the weaponization of public data. Realizing that true digital anonymity requires systematically degrading the confidence of global surveillance algorithms.
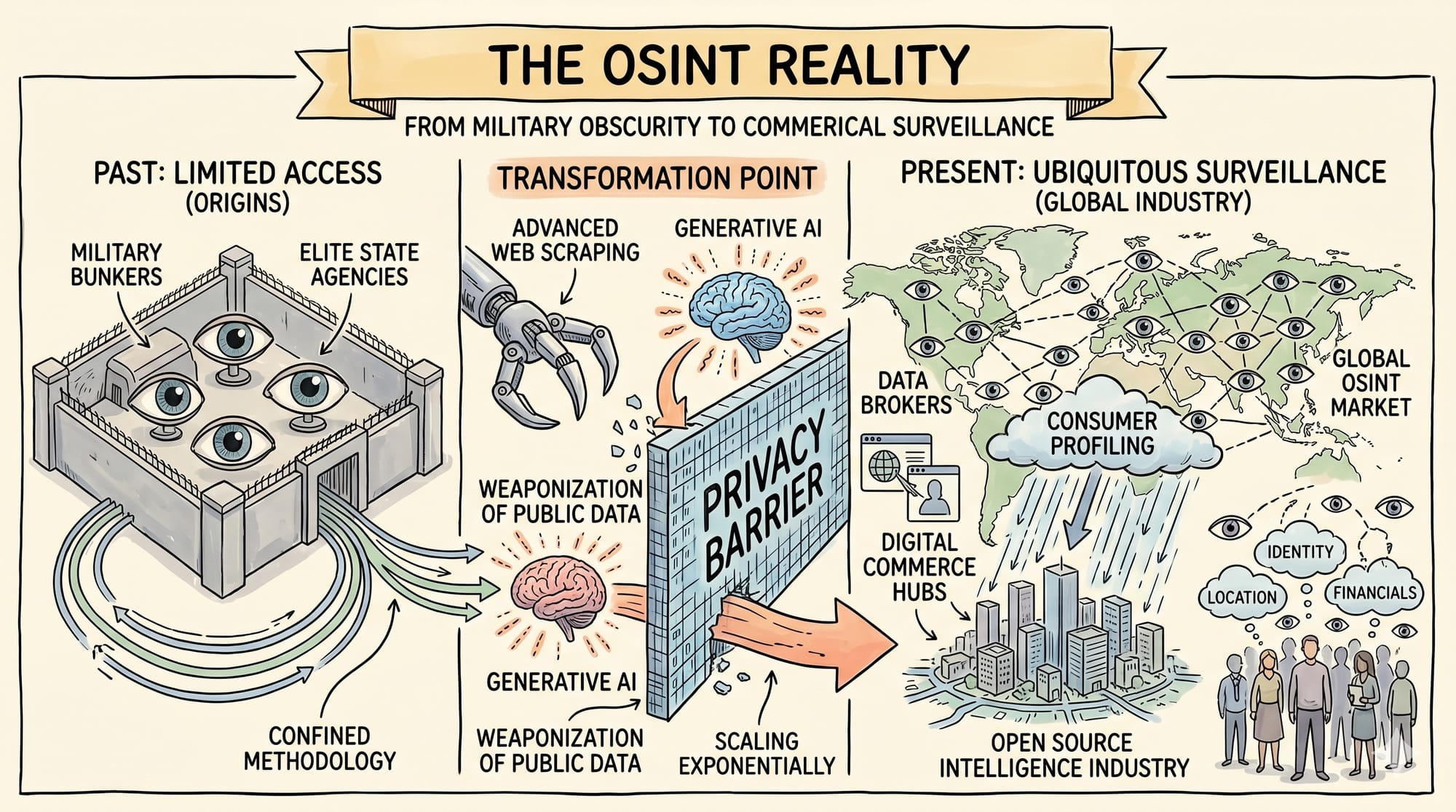
The OSINT Reality
The digital landscape has fundamentally transformed privacy from default obscurity to ubiquitous commercial surveillance.
Open source intelligence was originally a methodology strictly confined to military operations and elite state agencies.
Today, it is a massive global industry driven by advanced web scraping and generative artificial intelligence.
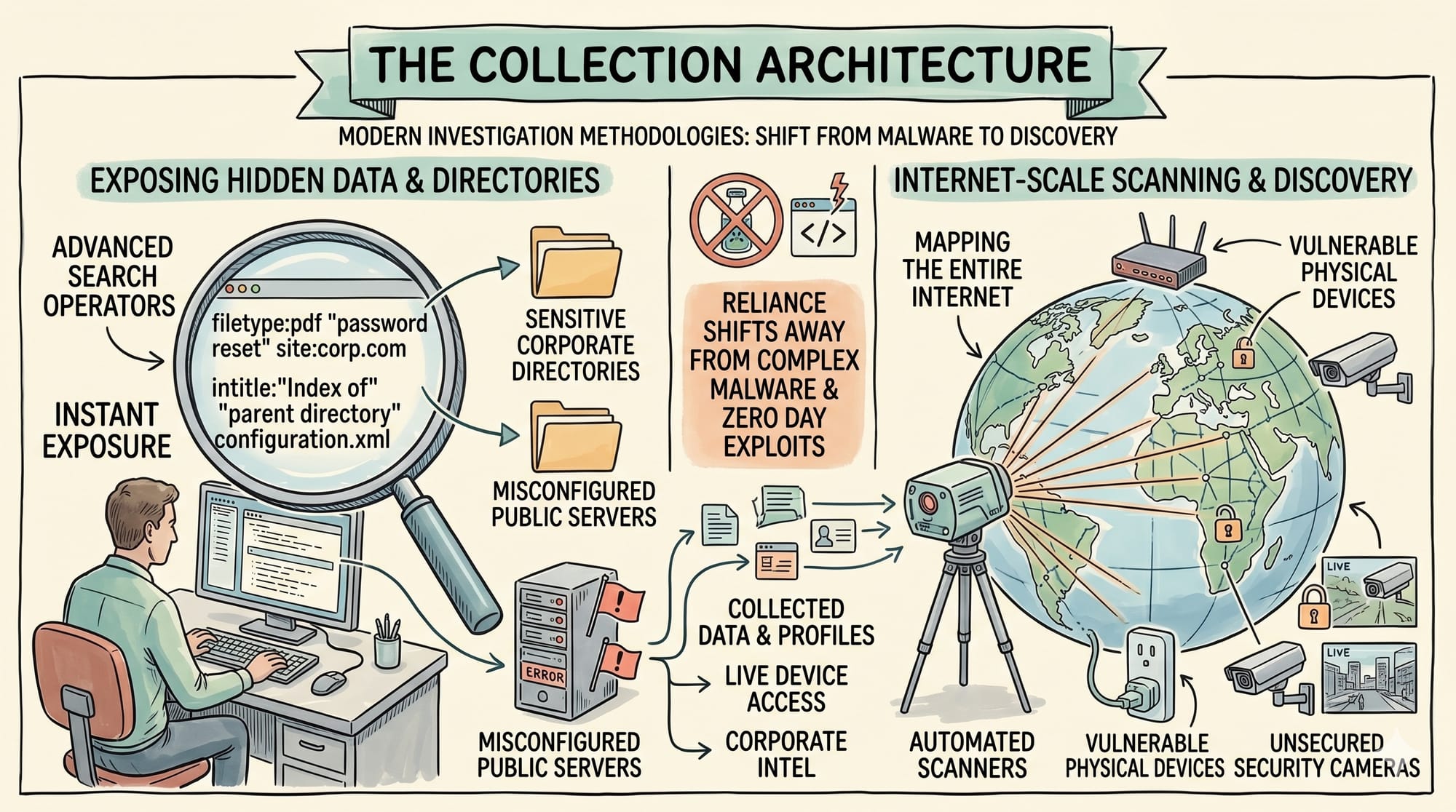
The Collection Architecture
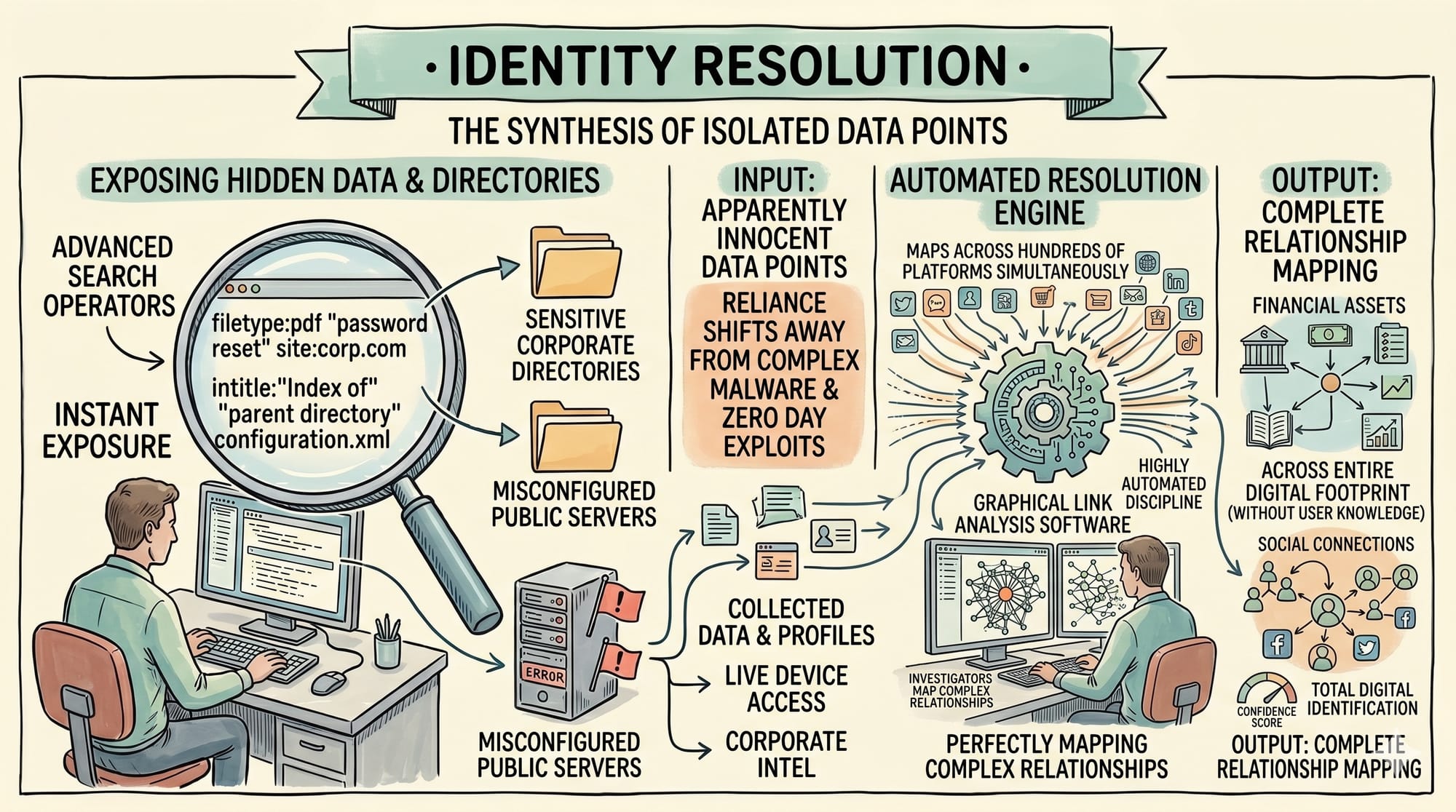
Modern investigators no longer rely on complex malware or zero day exploits to compromise a specific target.
They utilize advanced search operators to instantly expose sensitive corporate directories and misconfigured public servers.
Automated network scanners map the entire internet to locate vulnerable physical devices and unsecured security cameras.
Identity Resolution
Identity resolution is currently a highly automated discipline that maps a single data point across hundreds of platforms simultaneously.
A seemingly innocent username or secondary email address can instantly reveal your entire digital footprint without your knowledge.
Investigators use graphical link analysis software to perfectly map the complex relationships between your financial assets and social connections.
Strict Compartmentalization
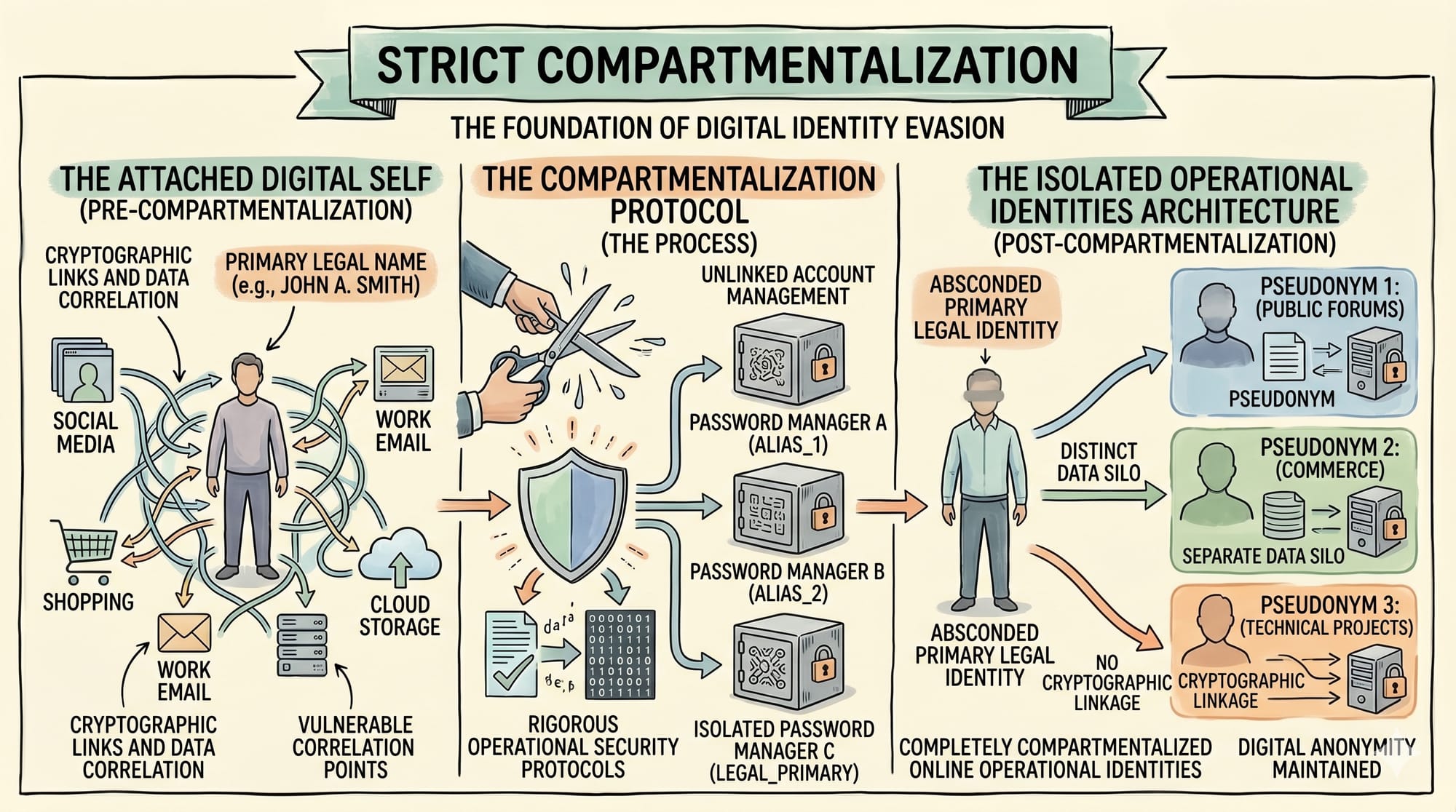
The absolute foundation of digital evasion is the strict compartmentalization of your online operational identities.
You must completely sever the cryptographic links between your primary legal name and your peripheral digital activities.
This requires creating distinct pseudonyms managed through rigorous operational security protocols and isolated password managers.
Data Falsification
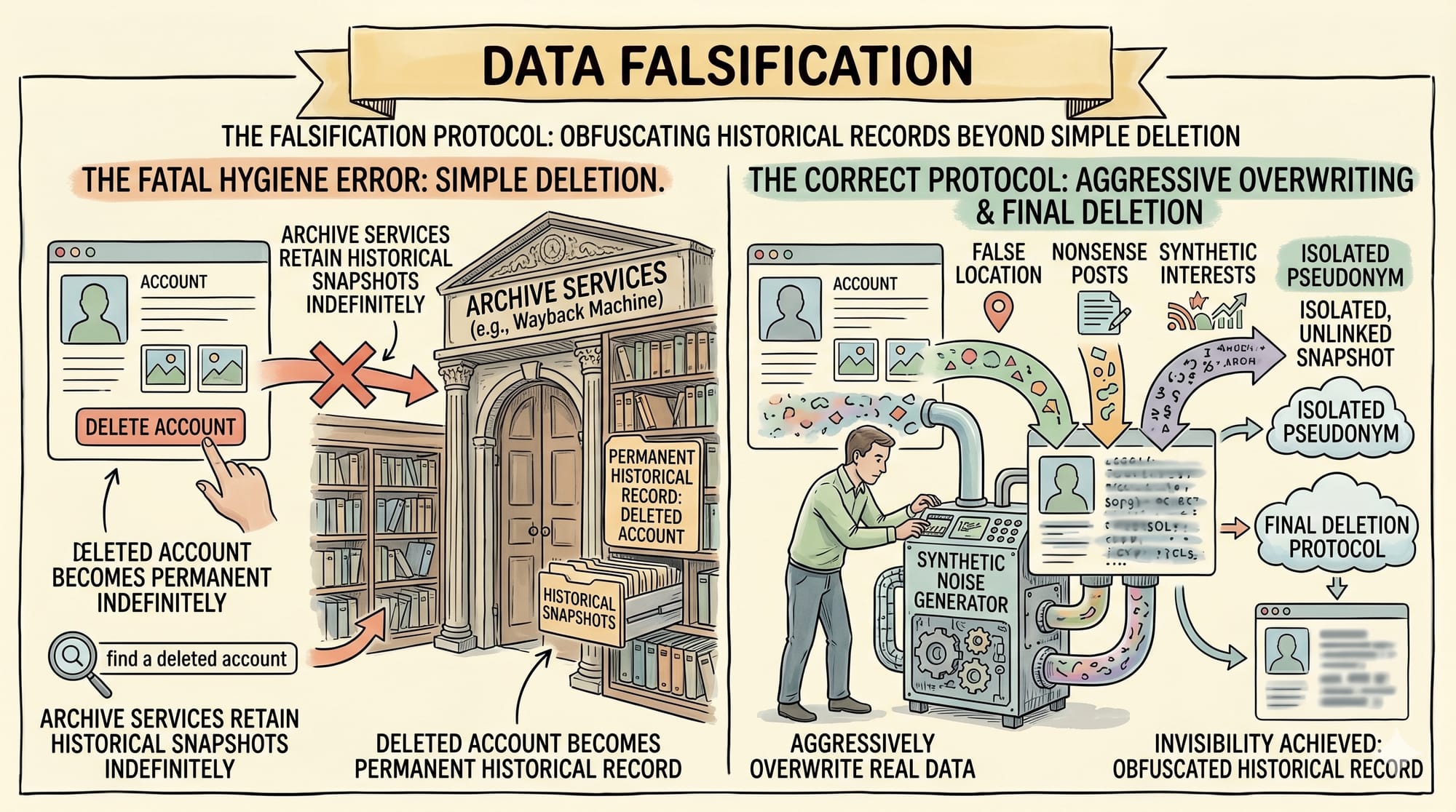
A massive error in standard privacy hygiene is the simple deletion of an exposed social media account.
Archive services retain historical snapshots indefinitely, meaning a deleted account simply becomes a permanent historical record.
You must aggressively overwrite accurate data with synthetic noise before initiating the final deletion protocol.
The Broker Ecosystem
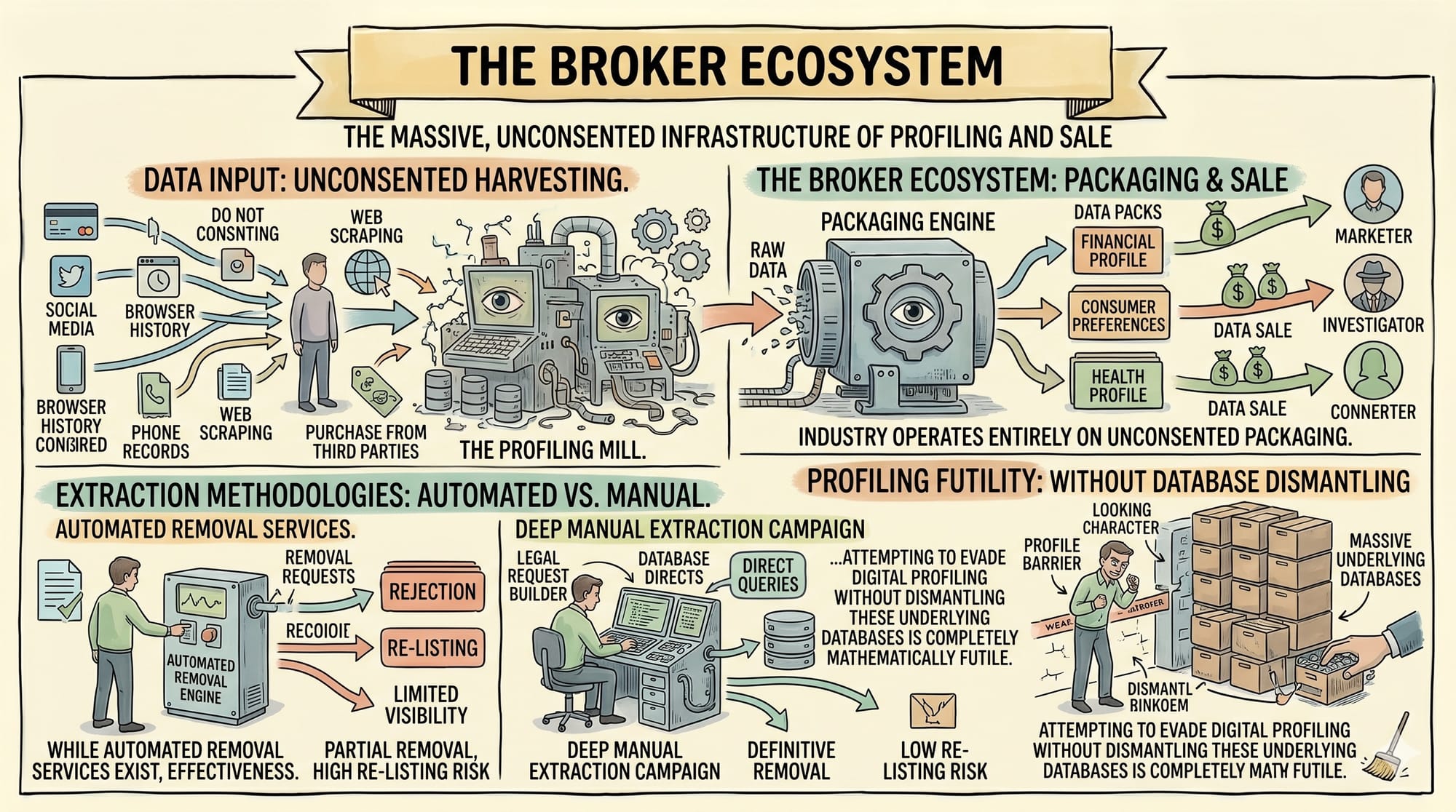
The data broker industry operates entirely on the unconsented packaging and sale of your personal information.
Attempting to evade digital profiling without dismantling these underlying databases is completely mathematically futile.
While automated removal services exist, manual extraction campaigns remain the absolute most effective methodology for high risk individuals.
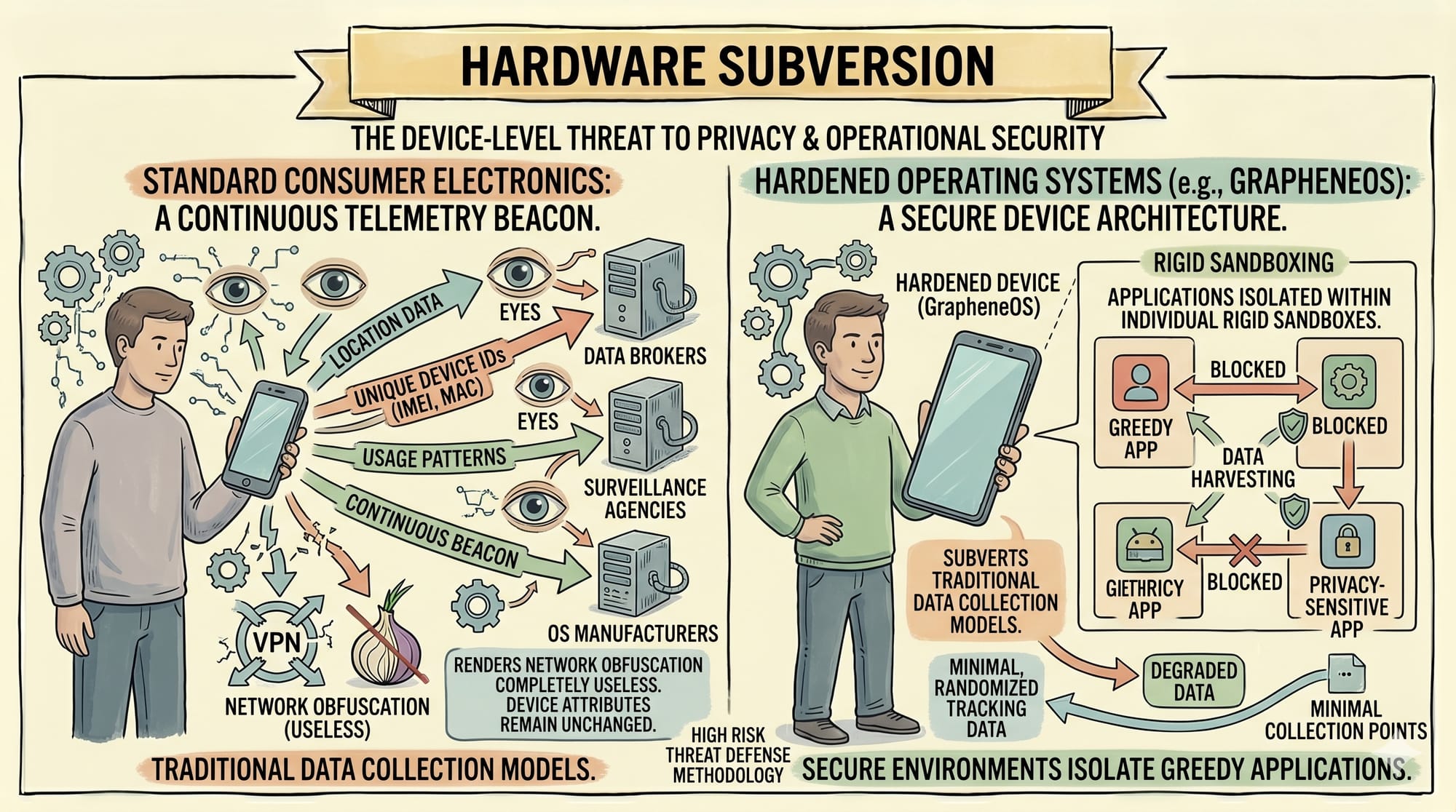
Hardware Subversion
Standard consumer electronics function as continuous telemetry beacons that render network obfuscation completely useless.
Evading device level tracking requires migrating to hardened operating systems like GrapheneOS that subvert traditional data collection models.
These secure environments isolate greedy applications within rigid sandboxes to prevent cross application data harvesting.
Network Obfuscation
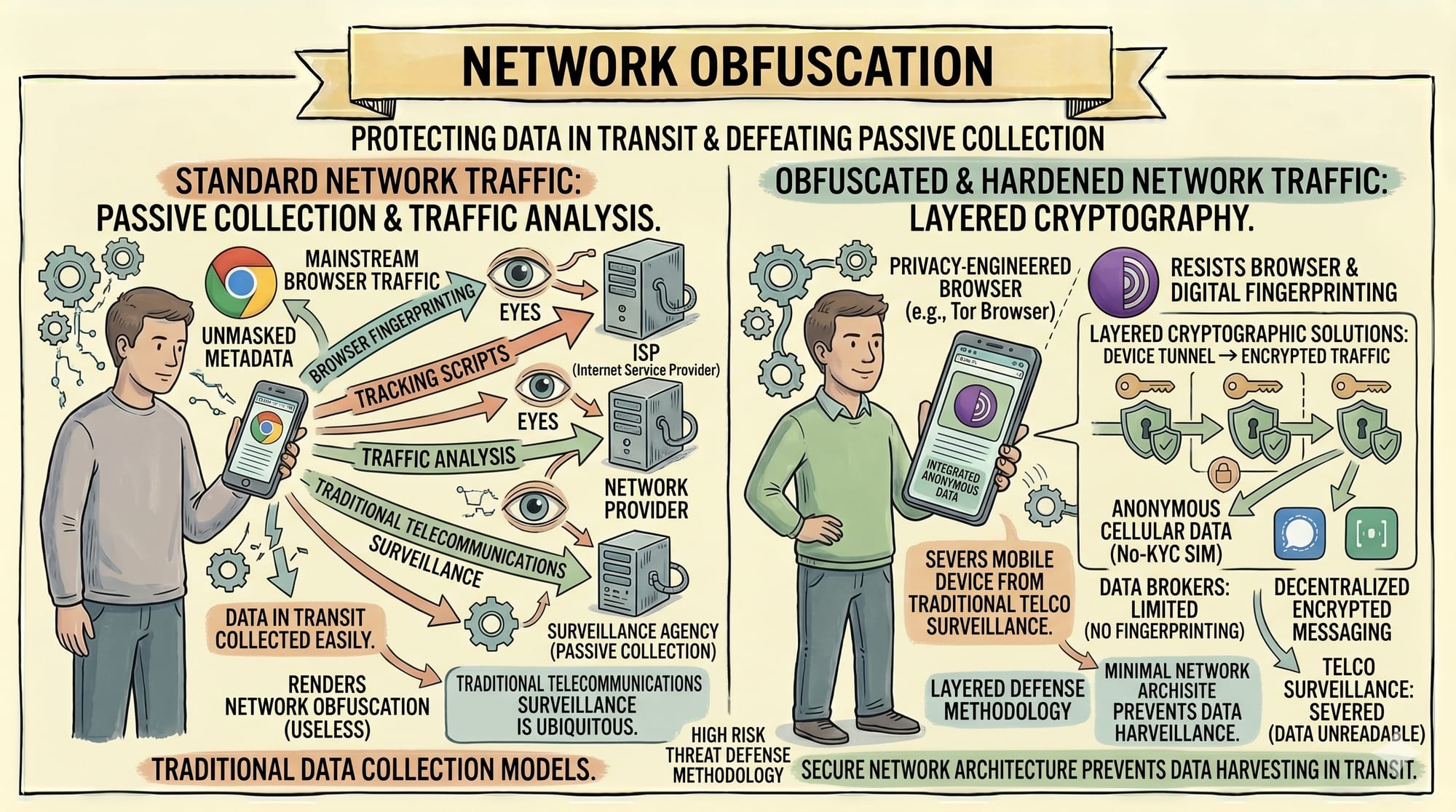
Protecting data in transit requires layered cryptographic solutions to defeat passive network collection.
You must abandon mainstream browsers and adopt platforms explicitly engineered to resist digital fingerprinting and advanced tracking scripts.
Combining anonymous cellular data with decentralized encrypted messaging severs your mobile device from traditional telecommunications surveillance.
Physical Abstraction
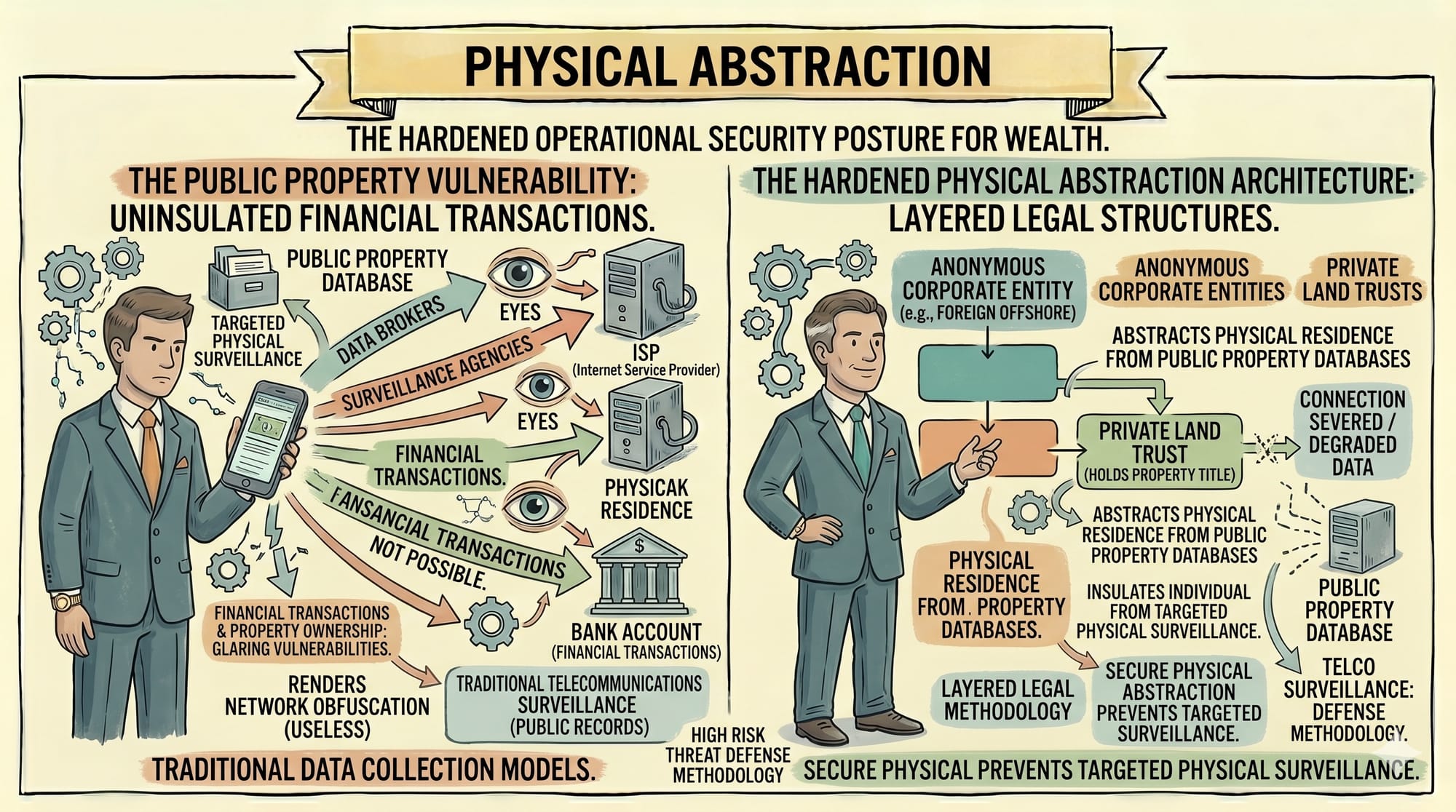
Financial transactions and property ownership are the most glaring vulnerabilities in any operational security posture.
To purchase property invisibly, wealthy individuals employ complex legal structuring utilizing anonymous corporate entities and private land trusts.
This abstracts their physical residence from public property databases and insulates them from targeted physical surveillance.
Counter AI Strategies
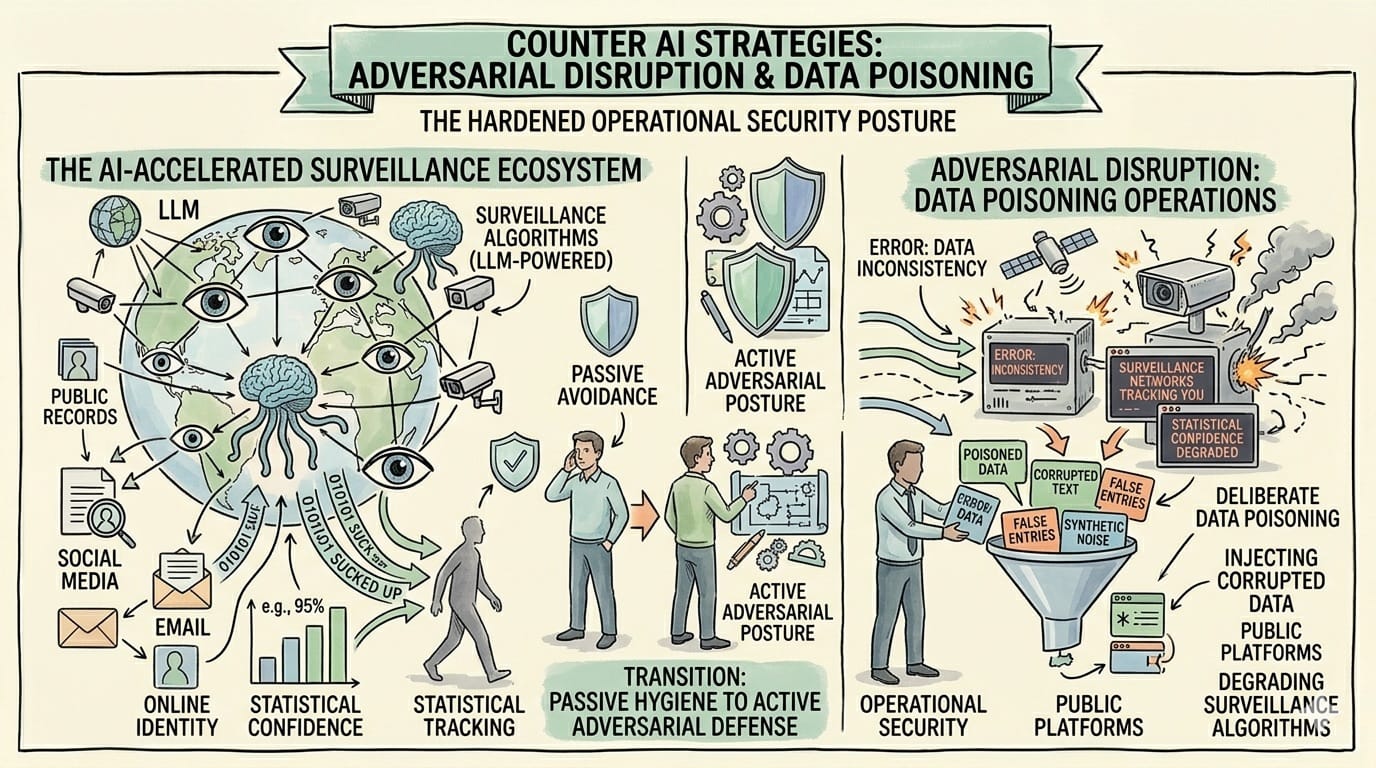
The rapid integration of large language models into the surveillance ecosystem has radically accelerated automated data extraction.
Privacy advocates must transition from passive avoidance to active adversarial disruption through deliberate data poisoning operations.
By injecting corrupted data into public platforms, you actively degrade the statistical confidence of the surveillance networks tracking you.
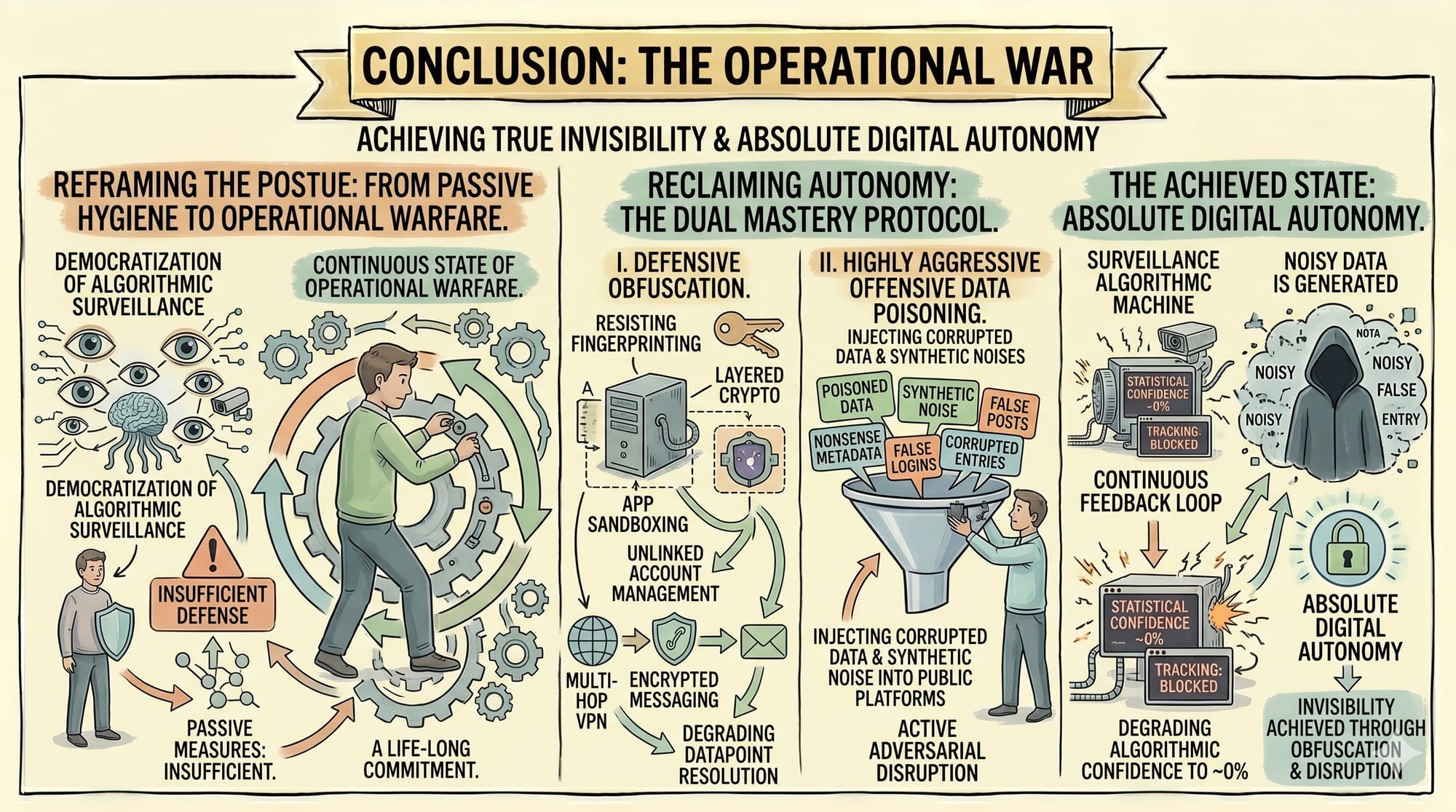
Conclusion: The Operational War
Achieving true invisibility is not a singular technological achievement but a continuous state of operational warfare.
The democratization of algorithmic surveillance dictates that passive privacy measures are entirely insufficient for the modern executive.
Reclaiming your absolute digital autonomy requires mastering both defensive obfuscation and highly aggressive offensive data poisoning.